Abstract
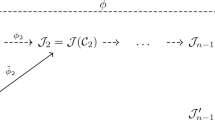
We give algorithms to compute \((\ell ,\ell )\)-isogenies between Jacobians of genus 2 curves and products of elliptic curves in time of \({\tilde{O}}(\ell ^2)\) basic field operations, where \(\ell \) is an odd prime different from the characteristic of the field. The method relies on the notion of a normal Weil set of Weil functions due to Shepherd-Barron, and works for the case of computing \((\ell ,\ell )\)-isogenies between Jacobians of genus 2 curves.

Similar content being viewed by others
References
Castryck W., Decru T.: An efficient key recovery attack on SIDH. In: Hazay C., Stam M. (eds.) Advances in Cryptology-EUROCRYPT 2023. https://doi.org/10.1007/978-3-031-30589-4_15.
Cosset R., Robert D.: Computing \((\ell,\ell )\)-isogenies in polynomial time on Jacobians of genus \(2\) curves. Math. Comput. 84(294), 1953–1975 (2015).
Couveignes J., Ezome T.: Computing functions on Jacobians and their quotients. LMS J. Comput. Math. 18(1), 555–577 (2015).
Decru T., Kunzweiler S.: Efficient computation of \((3^n,3^n)\)-isogenies. In: El Mrabet N., De Feo L., Duquesne S. (eds.) Progress in Cryptology - AFRICACRYPT 2023. https://doi.org/10.1007/978-3-031-37679-5_3.
Howe E.W., Leprevost F., Poonen B.: Large torsion subgroups of split Jacobians of curves of genus two or three. Forum Math. 12(3), 315–364 (2000).
Jao D., Azarderakhsh R., Campagna M., Costello C., De Feo L., Hess B., Hutchinson A., Jalali A., Karabina K., Koziel B., LaMacchia B., Longa P., Naehrig M., Pereira G., Renes J., Soukharev V., Urbanik D.: Supersingular isogeny key encapsulation. https://sike.org/files/SIDH-spec.pdf.
Jao D., De Feo L.: Towards quantum-resistant cryptosystems from supersingular elliptic curve isogenies. In: PQCrypto, Lecture Notes in Computer Science, vol. 7071, pp. 19–34 (2011).
Kani E.: The existence of curves of genus 2 with elliptic differentials. J. Number Theory 64(1), 130–161 (1997).
Kuhn R.M.: Curves of genus \(2\) with split Jacobian. Trans. Am. Math. Soc. 307(1), 41–49 (1988).
Lubicz D., Robert D.: Fast change of level and applications to isogenies. Res. Number Theory 9, Article number: 7 (2023).
Maino L., Martindale C. Panny L. Pope G., Wesolowski B.: An direct key recovery attack on SIDH. In: Hazay, C., Stam, M. (eds) Advances in Cryptology - EUROCRYPT 2023. https://doi.org/10.1007/978-3-031-30589-4_16.
Milio E.: Computing isogenies between Jacobians of curves of genus \(2\) and \(3\). Math. Comput. 89, 1331–1364 (2020).
Mumford D.: On the equations defining abelian varieties. I. Invent. Math. 1, 287–354 (1966).
Robert D.: Breaking SIDH in polynomial time. In: Hazay C., Stam M. (eds.) Advances in Cryptology - EUROCRYPT 2023. https://doi.org/10.1007/978-3-031-30589-4_17.
Shepherd-Barron N.: Thomae’s formulae for non-hyperelliptic curves and spinorial square roots of theta-constants on the moduli space of curves. Algebraic Geom. (2008). arXiv:0802.3014.
Smith B.: Explicit endomorphisms and correspondences. Ph.D. thesis, University of Sydney (2006).
Smith B.: Computing low-degree isogenies in genus \(2\) with the Dolgachev-Lehavi method. AMS Contemp. Math. 574, 159–170 (2012).
Tian S.: Cover attacks for elliptic curves over cubic extension fields. J. Cryptol. 36(3), 32 (2023).
Tian S.: Translating the discrete logarithm problem on Jacobians of genus \(3\) hyperelliptic curves with \((\ell ,\ell ,\ell )\)-isogenies. J. Cryptol. 34(3), 32 (2021).
Vélu J.: Isogénies entre courbes elliptiques. C. R. Acad. Sci. Paris Série 273, A238–A241 (1971).
Acknowledgements
I sincerely thank the anonymous referees for their comments and corrections. This work was funded by the National Key Research and Development Program (Grant No. 2022YFB2702700).
Author information
Authors and Affiliations
Corresponding author
Additional information
Communicated by A. Enge.
Publisher's Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Appendix: algorithms for \((\ell ,\ell )\)-isogeny
Appendix: algorithms for \((\ell ,\ell )\)-isogeny
In this appendix, we give two algorithms for computing the curves and rational functions in Theorems 3 and 4, respectively. In these algorithms, when we compute algebraic forms of \((\ell ,\ell )\)-isogenies, we implicitly assume, without mentioning it, that the characteristic p of the field \({\mathbb {F}}_q\) is larger than \( 3\ell +1\). If this is not the case, we have to use a strategy based on p-adic methods [3, Section 6].
We fix the following notation. For a field extension L/K and a formal series \(s\in L((t))\), we also denote by \(\text {tr}_{L/K}(s)\) the formal series obtained by keeping t fixed and applying \(\text {tr}_{L/K}\) to each coefficient of s.





Rights and permissions
Springer Nature or its licensor (e.g. a society or other partner) holds exclusive rights to this article under a publishing agreement with the author(s) or other rightsholder(s); author self-archiving of the accepted manuscript version of this article is solely governed by the terms of such publishing agreement and applicable law.
About this article
Cite this article
Tian, S. Computing gluing and splitting \((\ell ,\ell )\)-isogenies. Des. Codes Cryptogr. (2024). https://doi.org/10.1007/s10623-024-01413-x
Received:
Revised:
Accepted:
Published:
DOI: https://doi.org/10.1007/s10623-024-01413-x